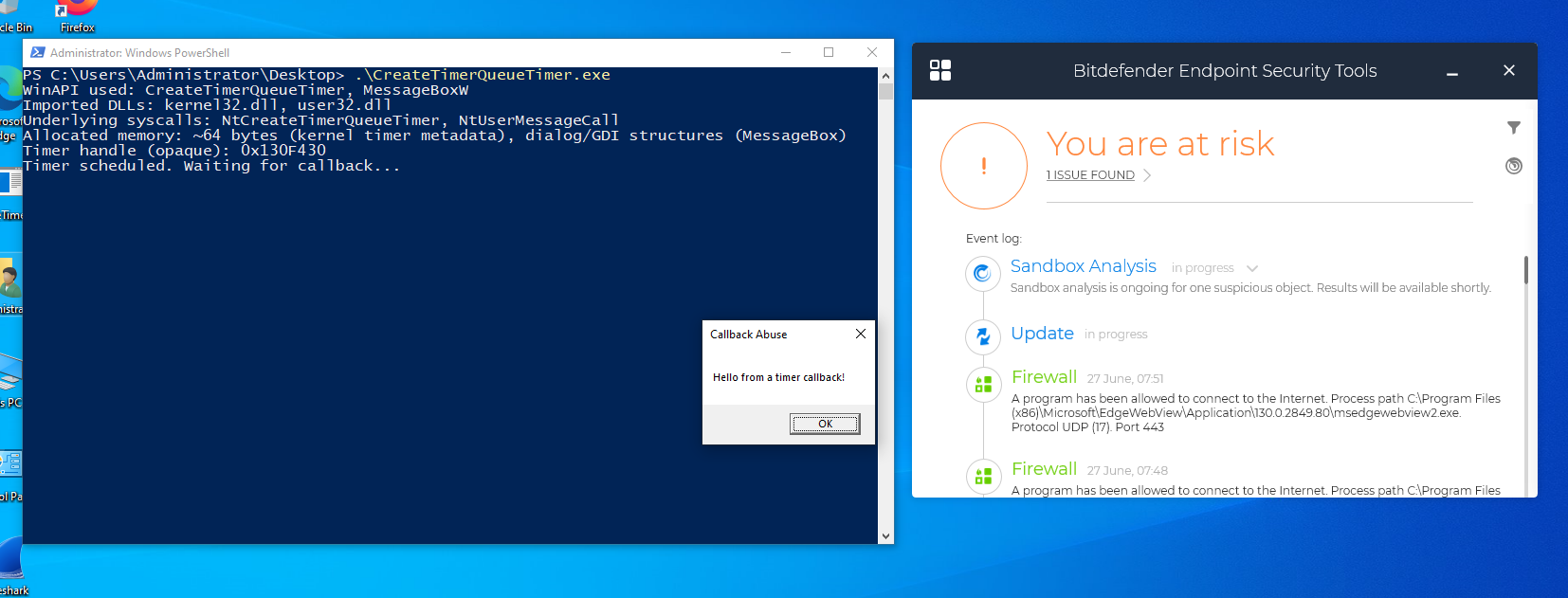
Callback Abuse: is the technique of handing a pointer to your own code, the “callback”, into a legitimate system or library function so that, when a normal event or
condition occurs, that function unwittingly “calls back” into your malicious logic. By doing so you piggy-back on trusted infrastructure, timers, GUI loops, I/O
completions, exception handlers, so your code runs under the guise of normal behavior. This avoids creating new threads or processes and dramatically reduces the
noise defenders see, making your payload far stealthier.
This inversion of control is what makes callbacks so powerful:
- Event-driven flow: Your code runs only when it matters (Ex: a timer fires, a window receives a message, an I/O completes).
- Thread reuse: Because the operating system or library already owns a pool of threads, you rarely need to create one yourself.
-
Stealth: Since no explicit
CreateThreadcall appears in your code, detection logic that keys off thread creation often misses the execution entirely.