What Is the WindowsAPI?
WinAPI known as "Windows Application Programming Interface", is the core native "toolbox" built into every copy of Microsoft Windows. It consists of thousands of functions, data structures,
and messaging systems organized into DLLs like kernel32.dll,user32.dll,
gdi32.dll, advapi32.dll, and ws2_32.dll.
These enable software to interact directly with the OS, performing tasks ranging from opening, creating, renaming files, drawing pixels, network connection and managing threads and hardware. If a program runs natively
on Windows and even many managed ones via interoperability layers, it almost certainly invokes WinAPI behind the scenes.
A Quick Origin History
Back in 1985, Windows 1.0 needed a safe, public doorway so third-party programmers could reach into the operating system without going through undocumented memory. Microsoft’s answer was the Windows API a documented bundle of C-style functions exported from system DLLs. As Windows evolved adding multitasking, networking, Unicode, 64-bit addressing, hardware Plug-and-Play, and layered security, the API kept rising, yet its heartbeat never changed, your function call jumps into a DLL, the DLL relays that request to the kernel, the kernel does the heavy lifting, and the result bubbles back to your code.
-
1985: Windows 1.0
WinAPI (often called Win16) debuts as a thin, 16-bit layer over MS-DOS.
-
1993: Windows NT 3.1
Win32 arrives, introducing a 32-bit address space and pre-emptive multitasking—the foundation of the modern Windows API still in use today.
-
1995-2000: Windows 95/98/ME
Win32 bridges consumer and business editions of Windows, adding support for long file names, Plug and Play hardware, and improved networking.
-
2001–Now: XP → Windows 10/11
Same core API powers every modern release, now alongside .NET, WinRT & UWP frameworks.
When Do You Actually Reach for WinAPI?
Make a classic Windows program
The moment you pop a window, write a file, or paint a pixel you’re using WinAPI.
Example: MessageBoxW(NULL, L"Hi!", L"Greeting", MB_OK);
Tweak processes, threads, or memory
Calls like CreateProcessW, SuspendThread, VirtualAlloc live in WinAPI.
Example: A loader that allocates memory with VirtualAlloc and runs shellcode
Build or break security
AV/EDR hooks watch WinAPI; red-team tools abuse the same calls (NtCreateFile, WriteProcessMemory).
Example: EDR flags suspicious WriteProcessMemory.
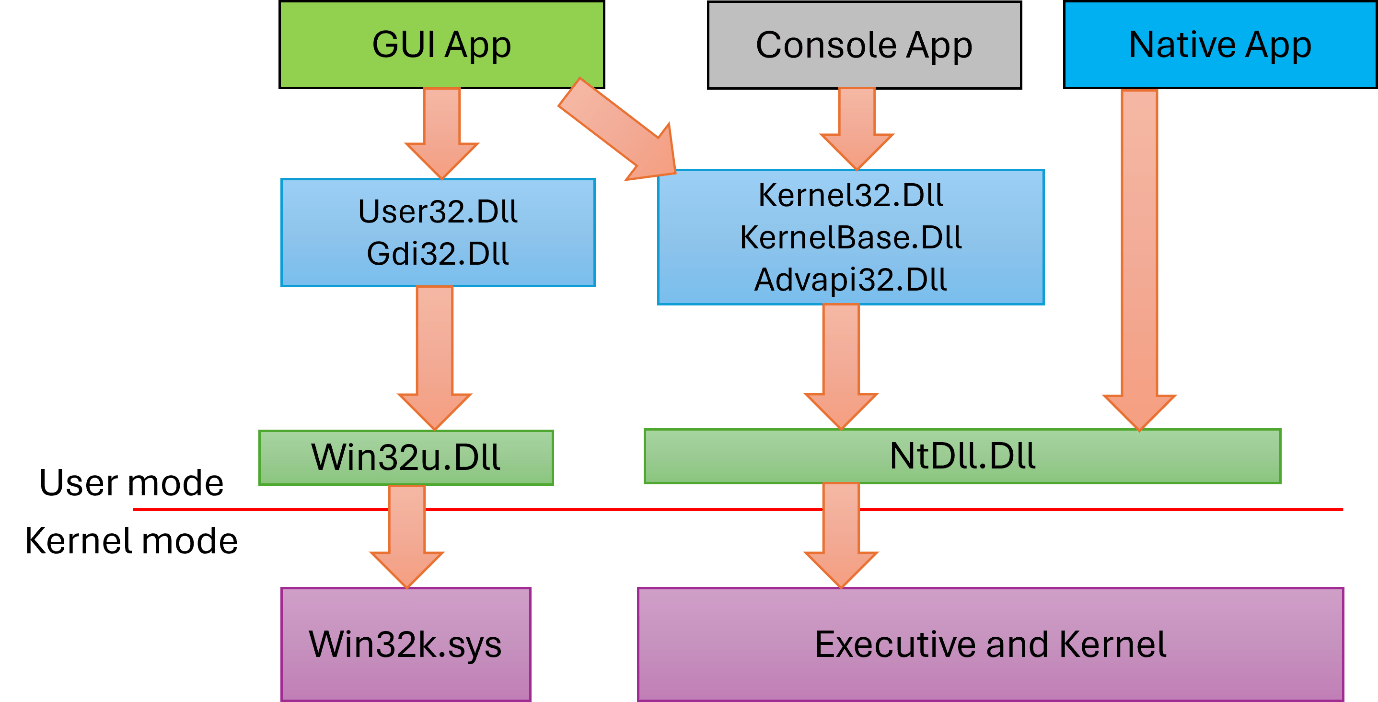
WinAPI Call Flow
Your Code
(Call a function, e.g. CreateFileW)
User-mode DLL
kernel32.dll/user32.dll/ws2_32.dll
(Checks parameters, may add convenience logic)
ntdll.dll
(Wraps request in a tiny “system call” stub)
Kernel(ntoskrnl.exe)
(Runs in Ring-0; talks to memory, drivers...etc)
Drivers / Hardware
(Disk writes, network packets, GPU frames)
Result Returns
(to your code)